Introduction :
Arivon Technologies enables to explore the latest trends on DATA MINING and utilize the maximum benefits of this Technology. Please visit www.arivontech.com for more details. Contact us sales@arivontech.com .
Data mining is defined as the process of extracting information from large set of data. In other ways we can say that data mining is mining knowledge from data.
The extracted information or knowledge can be used for some application are,
- Production Control
- Science Exploration
- Market Analysis
- Fraud Detection
- Customer Retention
DATA MINING KNOWLEDGE DISCOVERY:
Here in data mining knowledge discovery we have different type of steps such as,
- Data Cleaning: In first step, the process removing noise and inconsistent data.
- Data Integration: In second step, the process of combining multiple data sources.
- Data Selection: In third step, the process of retrieving relevant data to the task analysis from database.
- Data Transformation: In fourth step, the process of performing aggregation operations to transformed data into appropriate forms for mining.
- Data Mining: In fifth step, to extract data patterns we applied intelligent methods.
- Pattern Evaluation: In sixth step, data patterns are evaluated.
- Knowledge Presentation: In seven step, knowledge is represented.
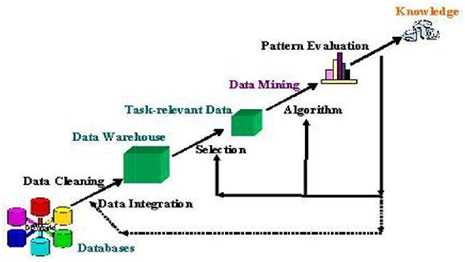
Fig: diagram for data mining knowledge discovery
DATA MINING SYSTEM CLASSIFICATION:
Here in data mining system classification we have so types such as,
- Statistics
- Machine Learning
- Database Technology
- Information Science
- Visualization
- Other Disciplines
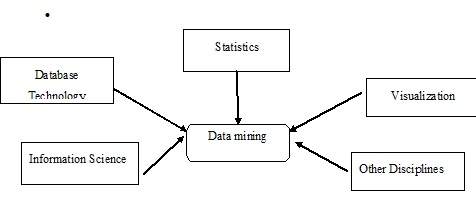
Fig: diagram for data mining system classification
Data mining is not an easy process, because these algorithms used can get very difficult and data is not available at same place it will available in different places. so it needs to be included from different heterogeneous data sources. These may create some problems. Here in this we have some major issues there such as
- Mining Methodology and User Interaction
- Performance Issues
- Diverse Data Types Issues
Mining methodology and user interaction:
- Mining different kinds of knowledge in databases
- Interactive mining of knowledge at multiple levels of abstraction
- Ad hoc data mining and Data mining query languages
- Incorporation of background
- Pattern evaluation
- Visualization and Presentation of data mining results
- Handling noisy or incomplete data
Performance Issues:
- Parallel, distributed, and incremental mining algorithms.
- Scalability and Efficiency of data mining algorithms.
Diverse Data Types Issues
- Mining information from different databases and global information systems.
- Handling of relational and complex types of data.
There are mainly two categories of functions concerned in Data Mining such as Descriptive, Classification and Prediction
Descriptive Function
It is deals with the common properties of data in the database. Some descriptive functions are
- Class/Concept Description
- Mining of Frequent Patterns
- Mining of Associations
- Mining of Correlations
- Mining of Clusters
Class/Concept Description
Class/Concept refers to the data to be associated with the classes or concepts. There are two functions in class/concept description such as
- Data Characterization: It refers to summarizing data of class under study.
- Data Discrimination: the process of classification or mapping of a class with some predefined group or class.
Mining of Frequent Patterns
Mining of frequent patterns will occur frequently in transactional data. some frequent patterns are such as
- Frequent Item Set: this one refers a set of items occurs together frequently.
- Frequent Subsequence: it refers the sequence of patterns occurs frequently.
- Frequent Sub Structure: it provides dissimilar structural forms.
Mining of Association
Associations are used in retail sales to identify patterns that are frequently purchased together. The process of detecting the relationship among data and determining association rules.
Mining of Correlations
Correlations is defined as the relations between two item sets to analyze that if they have positive, negative or no effect on each other.
Mining of Clusters
Cluster is defined as it is a process of forming a group of objects that are very similar.
Classification and Prediction
It is the process of finding a model that describes the concepts or data classes. based on the analysis of sets of training data it will derived. It is having different functions such as
- Classification (IF-THEN) Rules
- Decision Trees
- Mathematical Formulae
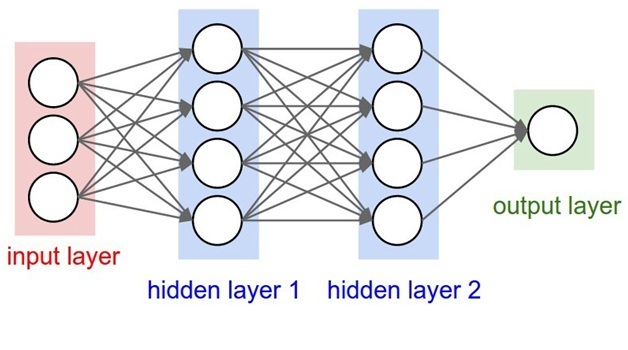
- Neural Networks